What to do after a PHI breach? Recovering after Disaster

HIPAA is long & challenging to read through and may seem time consuming to comply with which often leads to organizations putting off and delaying taking the steps to be HIPAA compliant. But whether it's through human error, a hacker or the lack of proper security measures, breaches of protected health information (PHI) do regularly occur. A PHI breach can be extremely costly - due to both potential HHS fines and the loss of trust or business from past clients. If you think there has been a breach of PHI within your organization, read below for what to do next.
Ready to simplify HIPAA compliance?
Join thousands of organizations that trust Accountable to manage their compliance needs.
Definition of a PHI Breach
First, let's define exactly what a PHI breach is according to HIPAA and the Breach Notification Rule. According to the Department of Health and Human Services (HHS), a breach is “an impermissible use or disclosure under the Privacy Rule that compromises the security or privacy of the protected health information.” Any unauthorized use or disclosure of PHI is assumed to be a breach unless the covered entity or business associate can show that there was a very small percentage chance that PHI was actually compromised.
Follow Contingency Plans
One standard that is laid out in the HIPAA Security Rule is that an organization needs to create a contingency plan. A contingency plan is essentially a coordinated plan with all the steps to recover systems, operations and data following the disaster. This would lay out what to do to restore the organization’s PHI that has been compromised and to maintain the critical daily operations of the company. Since this is one of the administrative safeguards under the Security Rule, this should already be created and implemented so the proper steps are taken quickly.
The key steps of a contingency plan would be identifying the location in the software or facility where the breach occurred, determining exactly what information was involved, and then containing the breach from any further growth. From that point, the breach would need to be reported to all the required parties before the necessary recovery efforts can be done. If you are a business associate, you will need to report the breach to the covered entity and other entities that you are under contract with.
Report the Breach
The HIPAA Breach Notification Rule lays out what is considered a breach and what steps need to be taken to notify patients and other entities after a breach of unsecured PHI occurs. When a breach occurs, the covered entity or business associate must notify all of the people who are reasonably believed to have been affected, as soon as possible after the breach. Companies should move to quickly notify patients and can be fined if they have not issued notifications within 60 days of their discovery of the breach.
Covered entities are also required to notify the HHS of the breach, the timeline on when they must do so depends on the amount of people that were affected by the breach. Here are the requirements that are different for the smaller versus larger breaches in PHI:
Breaches affecting less than 500 people:
For breaches that affected the information of less than 500 people, covered entities must notify the Office for Civil Rights (OCR) within 60 days of the end of the calendar year in which the breach was discovered. If there were separate breaches of information, they must be reported separately by incident.
Breaches affecting over 500 people:
If a PHI breach has affected the information of more than 500 people, there are a few additional expectations for their reporting of the breach. The OCR must be notified, as with the smaller breaches, however for the larger breaches it must be within 60 days of discovery rather than 60 days of the end of the year.
Due to the amount of people impacted, this information must be reported very quickly. Beyond this HHS report, breaches must also be reported to a major local print or broadcast media outlet in some situations. For the complete details on the reporting requirements, refer to the HHS website’s information.
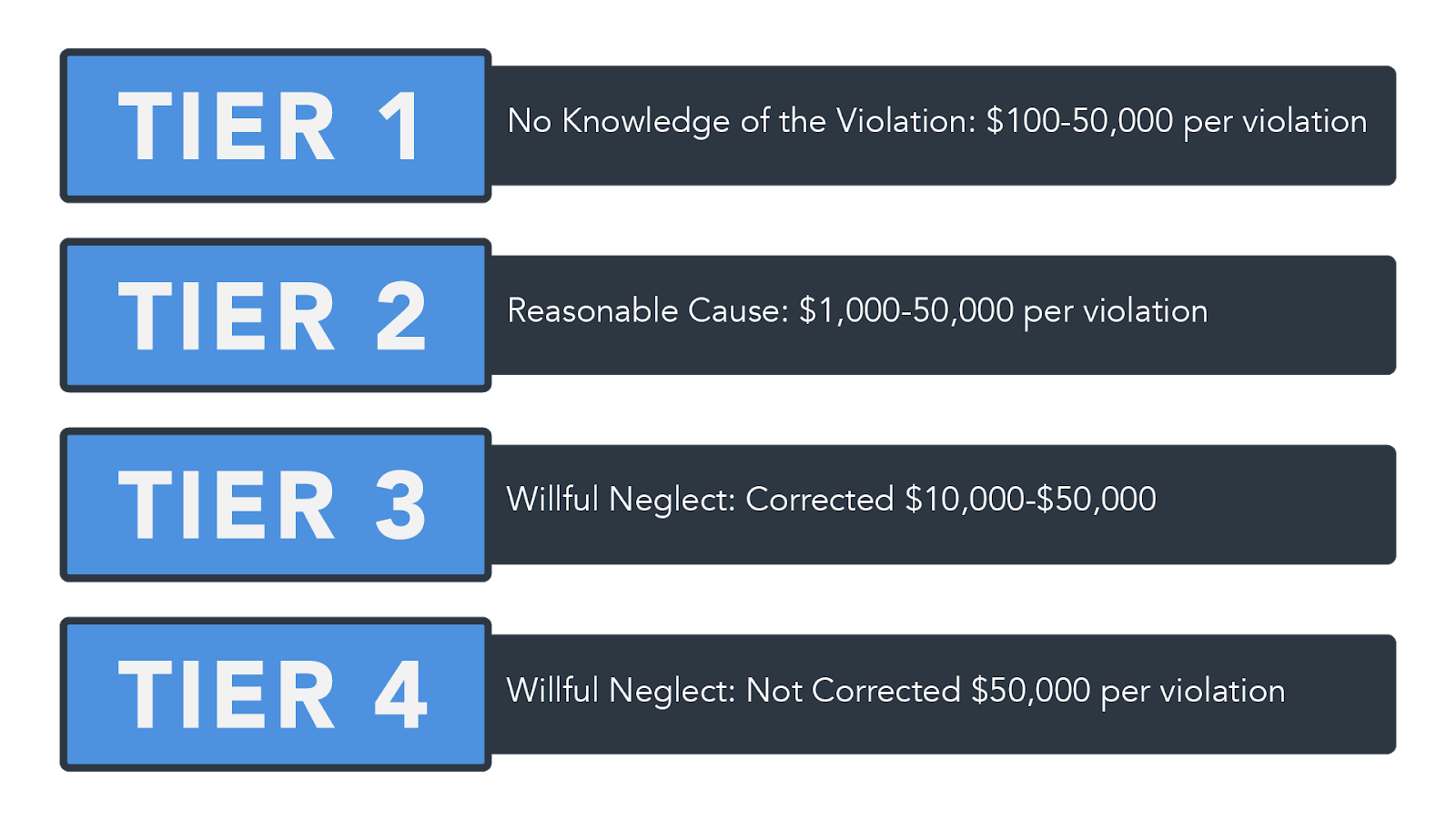
Understand potential HIPAA fines
HIPAA is a large and extensive law that presents high stakes for organizations that need to comply with all of the aspects of it. The costs and penalties for HIPAA noncompliance can range from $100 to $50,000 based on the perceived level of negligence.
First Tier: The covered entity did not know and could not have reasonably known of the breach. Generally, these range to $100 to $50,000 per incident up to $1.5 million in penalties.
Second Tier: The covered entity knew or by exercising reasonable diligence would have known of the violation, though they did not act with willful neglect. Fines for the second tier can range up to $1,000 to $50,000 per incident up to $1.5 million.
Third Tier: The covered entity “acted with willful neglect” and corrected the problems with a 30 day period of the breach. Penalties for the third tier can range from $10,00 - $50,000 per incident up to $1.5 million.
Fourth Tier: The covered entity acted with willful neglect and failed to make a timely correction. Fines start at $50,000 per incident up to $1.5 Million.
Address ways to prevent a recurrence
Although it is required for organizations to conduct regular risk assessments, a breach means that it is time to take a close and hard look at the current processes involving PHI to see weaknesses in how the information is being handled or stored. Under the HIPAA Security Rule mandates, organizations must conduct thorough assessments of all vulnerabilities of ePHI within their specific company.
Once a risk analysis has been completed, companies are responsible for implementing and any necessary corrective or preventive steps to address the weaknesses and risks. Even organizations that have taken steps to comply with HIPAA can experience breaches of PHI, which is an indicator that they should revamp their security controls and/or employee training to do a better job preventing a breach.
Many of the breaches that occur are due to human error mistakes like leaving a computer open and unattended or falling for phishing attempts. Preventing these types of mistakes is fairly easy if training and retraining new and veteran employees is a priority within the organization. Covered entities and business associates might also look into implementing a monitoring system so that they are able to track employee access to each file so that they are able to identify the responsible parties in the event of a future breach.
Ready to simplify HIPAA compliance?
Join thousands of organizations that trust Accountable to manage their compliance needs.



