Data Flow Mapping
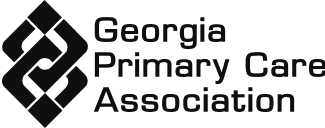
Understanding how Protected Health Information (PHI) moves through your organization is a foundational requirement of HIPAA compliance. Accountable's Data Flow Mapping uses AI to automatically map the flow of PHI across your systems, people, and vendors — making it effortless to visualize, document, and maintain an accurate picture of your data landscape.






What is Data Flow Mapping?
Data Flow Mapping is the process of identifying and documenting how PHI enters, moves through, and exits your organization. It covers the systems that store data, the people who access it, and the vendors who process it. HIPAA requires covered entities and business associates to understand where PHI lives — but building these maps manually is time-consuming and error-prone.
-
AI-Powered PHI Flow Discovery
Accountable's AI makes data flow mapping effortless by intelligently mapping your PHI landscape:
-
Automatically identify how PHI flows between systems, departments, and vendors
-
Visualize your entire data landscape in a clear, easy-to-understand diagram
-
Eliminate the guesswork — AI detects connections you might miss manually
-
-
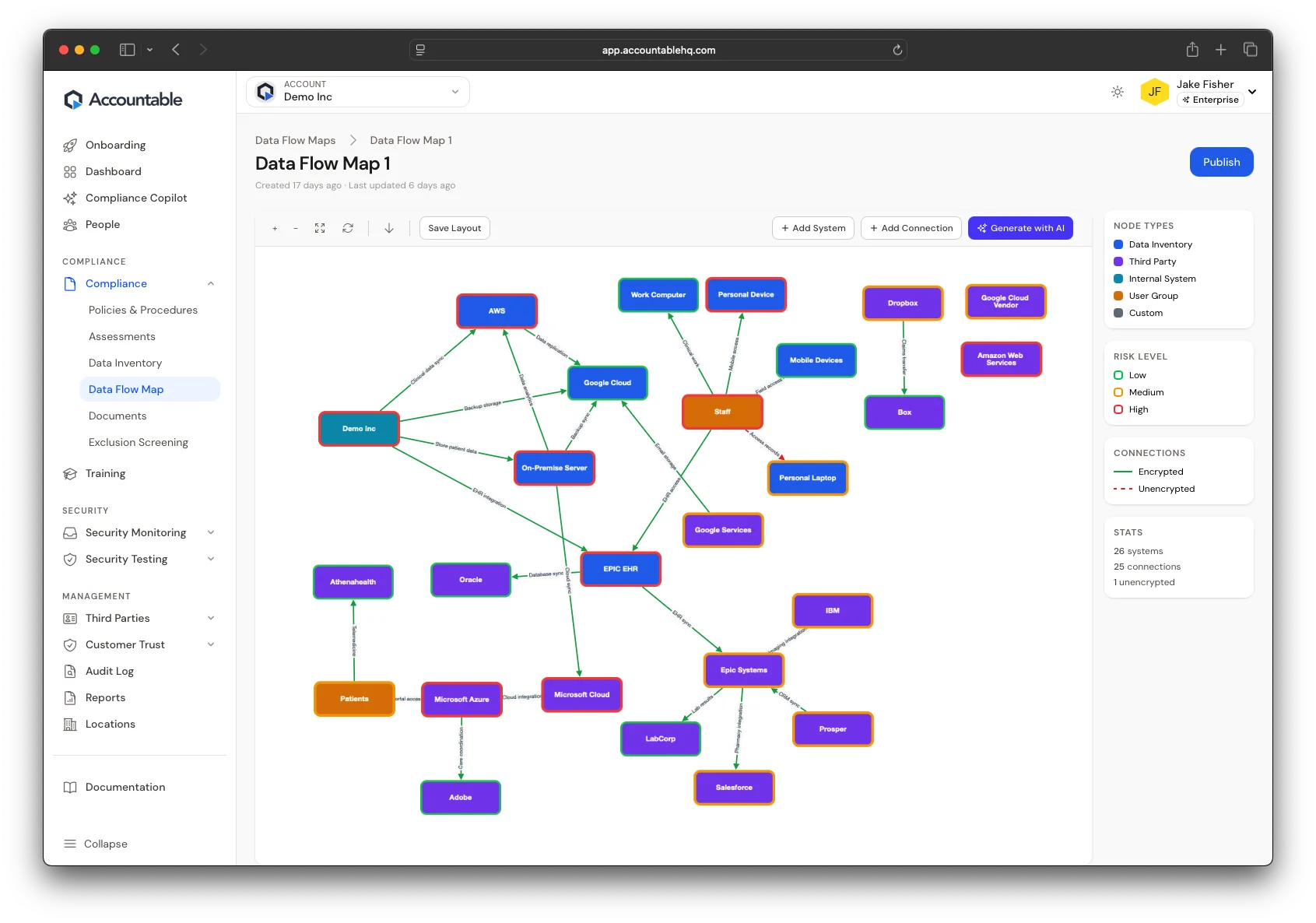
Stay Audit-Ready with Living Documentation
Your data flows change as your business grows. Accountable keeps your maps current and audit-ready:
-
Update your data flow maps as you add new systems, vendors, or processes
-
Export documentation for auditors, partners, or internal reviews
-
Tie data flows directly to your risk assessment and vendor management programs
-
Why Use Accountable for Data Flow Mapping?
Building a data flow map manually can take weeks. Accountable's AI does it in minutes — and keeps it up to date as your organization evolves.
-
AI-powered mapping that saves hours of manual documentation work
-
Clear visualization of PHI flows across people, systems, and vendors
-
Directly supports your HIPAA Security Risk Assessment and compliance program
Features to power any privacy, security, and risk management program
Compliance
Compliance Copilot New
AI agent that takes action
Security Risk Assessment
Identify & mitigate risks
Remediation Plan
Track corrective actions
Employee Dashboard
Monitor compliance progress
Policy Management
Centralized policy control
Data Inventory Management
Track & secure data
Policies & Procedures
Simplify compliance policies
Privacy Compliance Software
Automate privacy policies
Data Flow Mapping
Map PHI flows with AI
Federal Exclusion Screening
Automated OIG/LEIE screening
Compliance Hotline New
AI-powered incident reporting
Employee Training
HIPAA Training
Ensure HIPAA compliance
Security Awareness Training
Prevent cyber threats
Sexual Harassment Training
Foster workplace safety
Fraud, Waste, & Abuse Training
Learn best practices
Bloodborne Pathogens Training
Prevent exposure
Custom Training for Companies
Tailored employee learning
Vendor & Contract Management
Vendor Management System
Manage vendor compliance
Third-Party Security Monitoring
Track vendor security
Document Management System
Organize critical files
BAA Management System
Simplify agreement tracking
E-Signature
Secure digital signatures
Customer Trust
Incident Management
Report & resolve issues
HIPAA Seal of Compliance
Verify HIPAA compliance
Privacy Center
Comply with DSAR laws
Trust Center
Showcase compliance publicly
Data Breach Monitoring
Detect & respond to breaches
Multiple Location Management
Centralized franchise compliance
Frequently Asked Questions
Can't find the answer you're looking for? Please reach out to our team.